Virus Scan Before Upload on Website File
This article explains how to protect your website from malware upload past File Upload Form.
Statistics show that file upload vulnerabilities are WordPress'due south 3rd virtually common vulnerability type.
Hackers will often apply file upload vulnerabilities to spread malware, proceeds admission to spider web servers, perform attacks on visitors to a website, host illegal files, and much more than.
This guide will identify the risk factors of having unrestricted file uploads earlier explaining the virtually common types of file upload vulnerabilities.
Finally, we'll explain how to secure the WordPress file upload arrangement.
What are the adventure factors of unrestricted file uploads?
There are many adventure factors associated with unsecured file upload systems including:
Server-side attacks
If a hacker successfully places an executable file on your server, they may utilize it to launch server-side attacks.
For instance, if they upload a web shell, they may use it to take control of certain parts of your spider web server.

Exploiting file upload vulnerabilities also allows hackers to identify trojan horses, viruses, and other malicious files on your website.
Triggering vulnerabilities in server applications or libraries
Uploading a malformed file or one which masquerades as a different file blazon might trigger a vulnerability in certain pieces of server software.
1 well-known attack exploited a vulnerability in the image processing software ImageMagick. Hackers discovered they could execute arbitrary code by hiding information technology inside epitome files that would exist processed by ImageMagick.
This would potentially let the hacker to accept control of the server.
Hackers may also upload files to trigger vulnerabilities in real-time monitoring software. There was a recent vulnerability in Symantec antivirus software that could exist triggered by uploading a RAR file.
Triggering this vulnerability could result in retentiveness corruption on the server, potentially crashing certain programs or the server itself. Hackers could also employ this file upload exploit to crash the existent-time security monitoring, and then perform another kind of attack.
Client-side attacks
Uploading certain types of malicious files can make a WordPress website vulnerable to client-side attacks similar cross-site content hijacking and XSS attacks.
Hackers might as well be interested in uploading files that trigger vulnerabilities in the libraries or applications used by end-user devices. For example, at that place was a vulnerability in iPhone that caused a buffer overflow in LibTIFF.
Causing an administrator or webmaster to execute code
Malicious files including Windows viruses, Unix shell scripts, and Excel files may be uploaded if in that location are unrestricted file uploads.
A server administrator or webmaster might detect these files, so open them to make up one's mind what they are — executing the lawmaking and allowing malware onto your server.
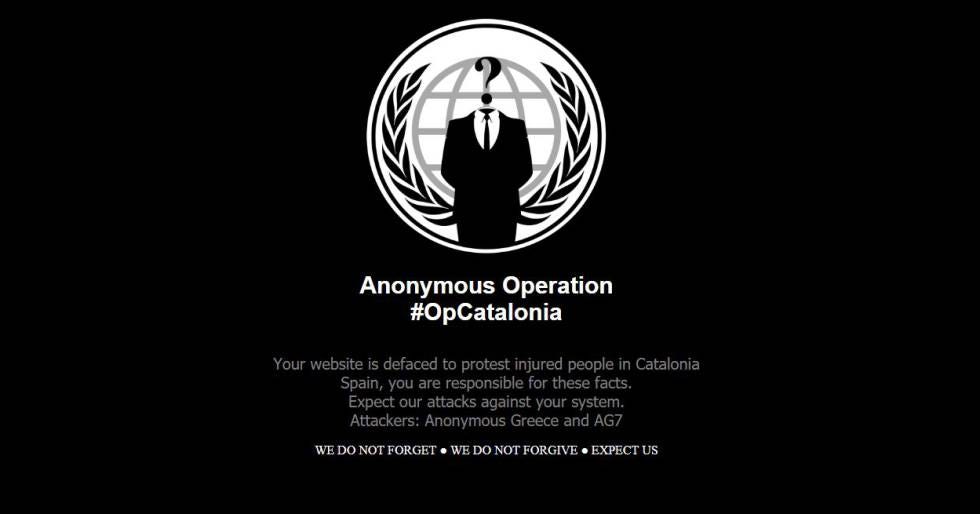
Hackers might be able to deface the website
If your website publishes user-uploaded content, allowing unrestricted file uploads may result in your website being defaced or used for a phishing assail.
The website's file storage organization may exist abused
Hackers often target unsecured file upload systems to store troublesome files. These files might include illegal software downloads, pornographic material, stolen intellectual property, malware, or data used by criminal organizations.
Hackers tin learn more about the server
An incorrectly secured file upload form may display mistake messages that give hackers data about the server's configuration. This information might include file paths or folder permissions.
Causing deprival of service attacks
Unsecured file upload forms may allow hackers to upload extremely large files or hundreds of files at once — performing a denial of service attack.
Types of file upload vulnerabilities
The nearly mutual types of file upload vulnerabilities include:
Unrestricted file upload with the unsafe type
This vulnerability occurs in systems where any blazon of file tin be uploaded to the server. Information technology also occurs when the file type is not fairly verified by the server.
This vulnerability could allow cybercriminals to upload whatever kind of executable file to the server.
In some cases, website owners might cheque the file extension of an uploaded file, merely fail to verify that it matches the contents of the file which has been uploaded.

This allows executable code to be subconscious within files with dissimilar extensions.
To avoid this vulnerability, the awarding must thoroughly bank check the files that are being uploaded and remove file types that can cause damage to the server.
The awarding should not rely solely on Content-Type HTTP header information when checking file types, but instead, utilise more detailed file checking processes.
Arbitrary file uploads
This vulnerability is created when a user is allowed to upload a file without beingness authenticated by the application.
The ability to upload should be restricted to authenticated users to forbid malicious individuals from uploading random files to your server.
Allowing arbitrary file uploads as well puts your site at greater take chances of a denial of service assail.
Uncontrolled resource consumption
Applications should place restrictions on the size of files that can be uploaded and the number of files that tin be uploaded.
Failure to practise so can allow users to upload very big files or thousands of modest files simultaneously, performing a DOS assail.
Files containing malware
If a website is parsing or inserting data from inside an uploaded file, it may exist vulnerable to files containing malware.
This type of attack often uses SQL injection attacks or attempts to get the organization to run some other arbitrary slice of code.
Protecting your WordPress website from file upload vulnerabilities
Hither are some simple steps yous can have to protect malware upload by file upload grade.
Simply allow specific file extensions
Past default, WordPress allows registered users to upload many types of files. This includes various types of image, audio, video, and certificate files.
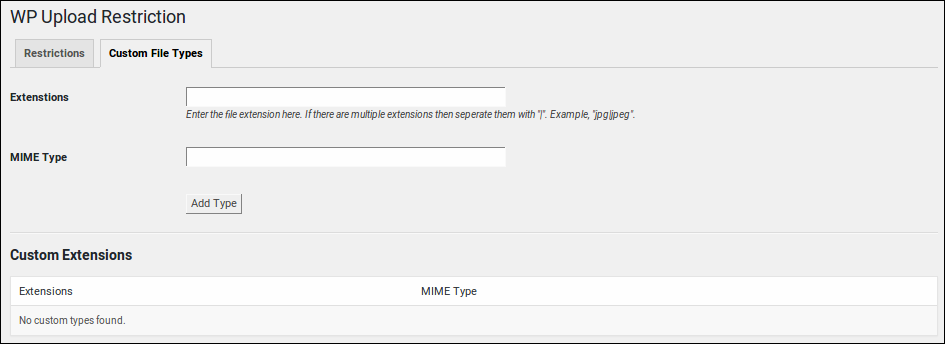
You can reduce the types of files that users tin upload by installing a plugin like WP Upload Restriction.
Use a WordPress form plugin that is secure
If you intend to take file uploads on your WordPress website, choose a well-known file upload plugin that has excellent security. At a minimum, the plugin should safeguard your form against common grade attacks like Cross-Site Request Forgery (CSRF) and Cross-Site Scripting (XSS) attacks.
Webmasters tin can also install a WordPress plugin that has real filetype detection, MIME analysis mapping, SVG sanitization, and a file upload debugger.
Such plugins make it easier to validate files and to create a whitelist of accepted MIME file types.
Reduce max file upload size
Preventing users from uploading large files will reduce the hazard of your file upload system being used for a DoS attack.
There are multiple ways to alter the maximum file upload size. The technique that works for yous will vary based on your server configuration and permissions.
If you have complete control over your server environment, you can alter the php.ini file to change the allowed size of file uploads.
Open your web server's php.ini file and alter theupload_max_filesize andpost_max_size directives. Once they have been updated, restart your HTTP server.

The snippet below volition change the maximum upload size to 4 megabytes.
Yous might likewise similar to include alter themax_execution_time directive, which rejects an upload if it has taken besides long to process. Some web servers will also allow you to create a php.ini file in your website's home directory.
upload_max_filesize = 4M post_max_size = 4M max_execution_time = 120
Adding php upload values to your .htaccess
Some web servers will also allow you lot to adjust PHP file upload settings via the .htaccess file in your WordPress installation's root directory. Add the following to modify upload sizes and max execution/input times:
php_value upload_max_filesize 4M php_value post_max_size 4M php_value max_execution_time 120 php_value max_input_time 120
Past default, WordPress doesn't allow public users to upload files. Even so, many WordPress administrators install plugins that contain file upload fields.
This is a potential vulnerability because you rely on the programmer of that plugin to safely handle this content. Your website will exist safer past only allowing certain types of registered users to upload files.
If yous need a form with an upload field to only be displayed to sure users, use a plugin similar to Restrict Content. It will permit you to restrict pages and portions of pages to certain types of users.
Add file execution restrictions using .htaccess
You can create a .htaccess file that restricts the types of files that can be executed from the uploads directory. For instance, the following .htaccess will just permit gif, jpeg, jpg, and png files to be executed:
deny from all gild deny,permit permit from all
This .htaccess must not be placed into the wp-content/uploads directory, because hackers could potentially overwrite it by uploading another file called .htaccess.
Place it in the directory to a higher place the uploads wp-content/uploads binder.
Identify your uploads binder outside of the server root
Creating a new folder for storing uploads tin can also help to amend file security. This folder should be created exterior of your website'due south public directory then hackers cannot manually execute the files they take uploaded via a website URL.
Read this brusque guide to learn how.
Randomize uploaded file names
Once hackers have managed to upload an executable file to your server, they may attempt to execute it using a web browser or command line.
One elementary trick to preventing hackers from running their files is to randomly rename it. You can read this brusque guide to learn how to randomize uploaded file names in WordPress.
Don't give data away
If a user uploads a file that triggers an error, make certain WordPress and PHP only display a very unproblematic error message.
Avoid displaying sensitive information similar file paths, WordPress installation details, or server configuration data. This information could be exploited past a hacker.
Hackers volition use many dissimilar techniques to obtain mistake messages from your website including uploading files that are in the wrong format, besides big, or which have a very long filename.
Add a CAPTCHA to your forms
Adding the WordPress CAPTCHA plugin to your site prevents cybercriminals from using your forms for DoS attacks.
Force uploads to be delivered in the correct file format
One of the biggest problems with handling uploads is that hackers can hide executable code inside image file formats.
You can overcome this issue past forcing the webserver to send the correct image headers before you display an image on your website.
For instance, the following will force the image to be displayed as a png, ignoring any executable code:
$data = file_get_contents('/dwelling/potentially-dangerous-file.png'); header('Content-Type: image/png'); header('Content-Length: '. strlen($data)); header('X-Content-Type-Options: nosniff'); echo $data; You can also process uploaded images using prototype manipulation software similar GD. By opening the epitome and re-saving it, you will remove any executable content.
You tin read more virtually security headers from the guide here.
Utilize a virus scanner on your server
Server-side virus scanners tin can detect file uploads that contain malware, trojans, and viruses. The virtually mutual application for this chore is ClamAV, an open-source antivirus engine.
Make sure it is configured to automatically browse uploads that are added to your spider web server.
Nosotros hope this article will help you to protect your site from malware upload past file upload grade.
gonzalezuncloyesseen.blogspot.com
Source: https://patchstack.com/articles/how-to-protect-site-from-malware-upload-by-file-upload-form/
0 Response to "Virus Scan Before Upload on Website File"
Postar um comentário